On March 30th, Google Quantum AI, along with co-authors from the Ethereum Foundation, Stanford, and UC Berkeley, published a bombshell paper that accelerated the quantum threat timeline by years. In it, they reported a 20x reduction in quantum resources to break the cryptographic primitives protecting every major blockchain.
At present, that puts half a trillion in BTC at risk, along with over $100 billion in Ethereum smart contract assets, and hundreds of billions in stablecoins, L2s, and tokenized real-world assets.
Here are four takeaways the crypto industry needs to reassess in light of these findings.
1. Quantum Risk is a Near-Term Problem
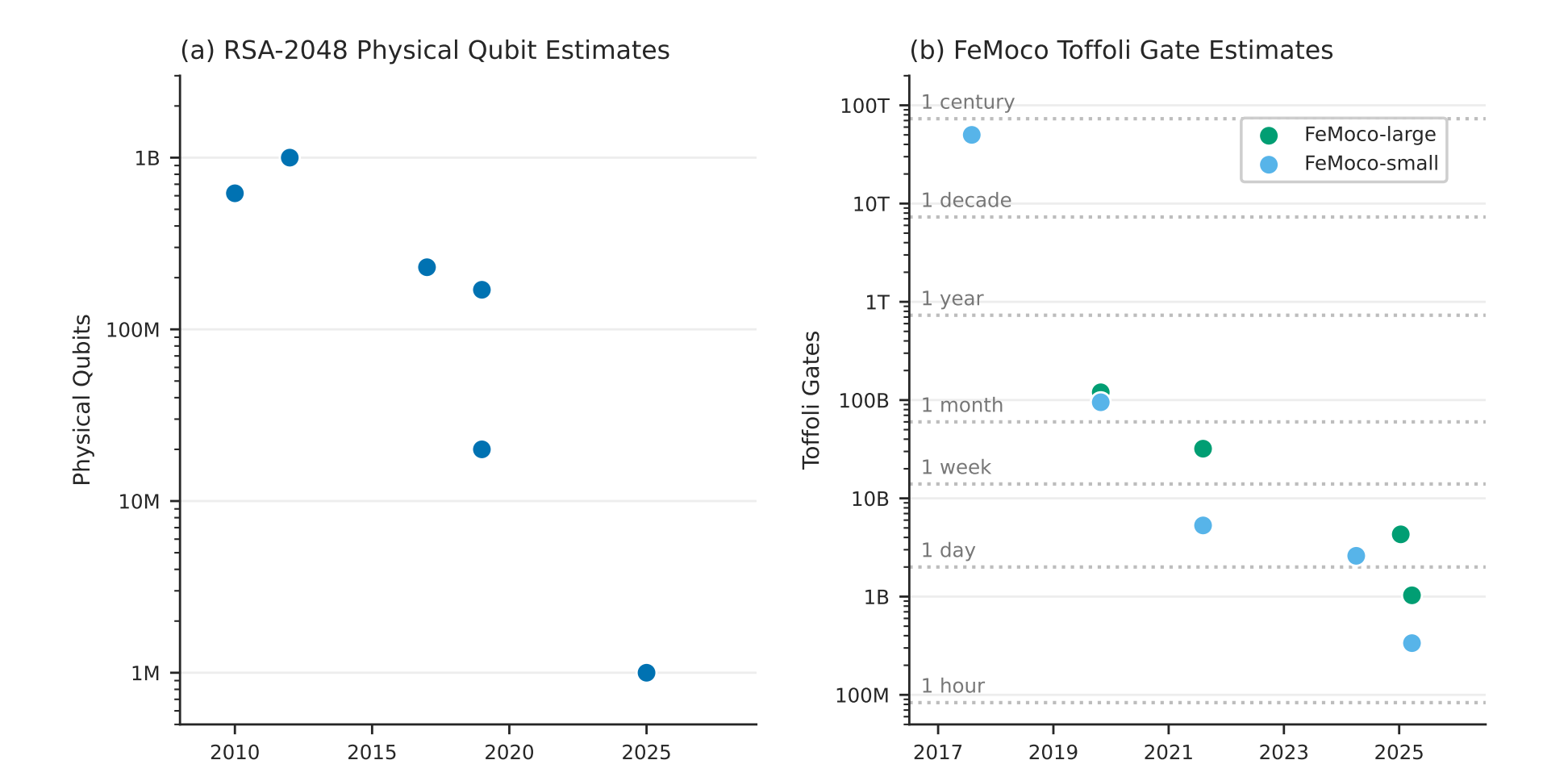
Before this paper, the prevailing consensus put the quantum threat to crypto somewhere in the late 2030s to 2040s. This paper accelerates the timeline significantly.
"My confidence in q-day by 2032 has shot up significantly. IMO there's at least a 10% chance that by 2032 a quantum computer recovers a secp256k1 ECDSA private key from an exposed public key.” — Justin Drake, Ethereum Foundation & co-author.
The headline finding is that breaking elliptic-curve cryptography that secures virtually every major blockchain requires 20x fewer quantum resources than previously estimated. Where prior research placed the threshold at around 9 million physical qubits, Google's team brought it under 500,000.
Perhaps more alarming is that a "primed" quantum computer could reverse-engineer a private key from an exposed public key in approximately 9 minutes. Today, no existing machine is capable of this feat – Google's most advanced chip has roughly 105 qubits, a fraction of the 500,000 the paper estimates – but a decade of algorithmic and error-correction advances continues to drive down resource estimates for quantum.
2. The Attack Surface Is Way Bigger Than Anyone Thought
Conversations around the quantum threat have centered almost exclusively on Bitcoin. This paper expands that to several different attack surfaces.
The authors identify 5 distinct attack vectors for Ethereum alone.
- Public keys are permanently exposed after a single transaction, with no way to rotate without abandoning the wallet.
- Smart contracts that govern over $200B in value, including those that back major stablecoins, rely on a small number of administrator accounts for critical functions. A quantum attack that cracks a private key can pause contracts, move funds, or rewrite logic.
- L2s and cross-chain bridges batch transactions off chain and submit proofs back to Ethereum. But those proofs rely on the same quantum-vulnerable cryptographic primitives as Ethereum. A compromised proof could convince the verifier that fraudulent transactions are legitimate to steal assets or inflate the token supply.
- Ethereum's consensus depends on validators staking ETH and voting on which transactions are valid. Those votes are authenticated using BLS signatures, which are vulnerable to quantum attacks. If enough validators are compromised, they could rewrite the chain's transaction history or halt finality entirely.
- Ethereum's data availability mechanism relies on KZG commitments whose security traces back to a one-time setup ceremony. A single quantum attack could recover the secret parameters from that ceremony, creating a permanent backdoor that undermines trust in the blockchain itself.

The paper extends well beyond Ethereum, mapping vulnerabilities across Zcash, Monero, Solana, Litecoin, stablecoins, and tokenized real-world assets. The total attack surface spans hundreds of billions of dollars, and is still growing. RWA tokenization alone is projected to increase nearly 10x by 2030, almost entirely on quantum-vulnerable chains.
3. Responsible Disclosure Got a New Playbook
The paper’s findings were sensitive enough that Google broke with its own precedent. Historically, Google has published its quantum cryptanalysis work in full. This time, they withheld the circuits entirely. The authors write:
"However, the escalating risk that detailed cryptanalytic blueprints could be weaponized by adversarial actors necessitates a shift in disclosure practices. Accordingly, we believe it is now a matter of public responsibility to share refined resource estimates while withholding the precise mechanics of the underlying attacks.”
Instead of publishing the quantum circuits, Google used Succinct's SP1 to generate a zero-knowledge proof that would allow anyone to cryptographically verify the circuits exist and work correctly, without revealing the exact design. The code and proofs are publicly available on GitHub for independent verification.
This is the first time zero-knowledge proofs have been used for the responsible disclosure of a novel vulnerability, and they will become the industry standard, as state-of-the-art algorithms will be withheld for safety. Zero-knowledge proofs offer a path towards scientific credibility without publicly exposing the underlying methods.
4. The Post-Quantum Cryptography Migration Clock Started
The authors’ closing message is unambiguous. They urge all cryptocurrency communities to immediately migrate to post-quantum cryptography (PQC), replacing vulnerable cryptographic primitives with algorithms that are secure against quantum computers.
NIST finalized its first post-quantum cryptography standards with lattice-based and hash-based signature schemes designed to resist quantum attacks. These standards are already in production. StarkNet, for example, uses hash-based cryptography and is considered quantum-resistant today.
Over the past few months, the crypto industry has mobilized around PQC. In January, Coinbase formed a quantum advisory board that includes paper co-authors Dan Boneh and Justin Drake. The Ethereum Foundation launched a dedicated post-quantum team, a 4-year upgrade roadmap, and a central hub at pq.ethereum.org.
However, migrating cryptographic infrastructure at scale is inherently slow. Even more so for decentralized protocols where every layer of the stack, from wallets, consensus mechanisms, smart contracts, to bridges and L2s, needs to be independently upgraded and tested, with zero margin for error. Ethereum’s roadmap spans four years and roughly seven hard forks. For Bitcoin, BIP-360 co-author Ethan Heilman has estimated a full upgrade could take up to seven years.
The Google Quantum AI paper is a detailed assessment that the quantum resources required to break cryptography are significantly lower than previously understood. The crypto industry has the standards, tools, and time to prepare, but that gap is closing. Fast.